How Poor Website Security Negatively Impacts SEO Rankings
“Website security” – let’s be honest here: when was the last time you seriously thought about it? When was the last time you or your SEO team spent two seconds on the latest security trends for websites?
Companies might be spending billions of dollars on SEO right now, but a significant percentage of enterprises with websites don’t even think about website security.
TABLE OF CONTENTS:
Why Web Security Is Important
As an entrepreneur, you’ve probably spent hundreds or even thousands of dollars over the years on marketing and SEO, but the weakest link in the digital marketing chain is clearly website security:
- A recent Google survey shows that Americans know less than they believe about website security: 55% of Americans over the age of 16 give themselves an A or B in online safety and security, but 70% of them wrongly identified what a safe website looks like.
- A Harris Poll survey from March 2019 shows that 97% of participating Millennials get at least one out of six questions on website security wrong.
- Ransomware attacks (a type of malicious software designed to block access to a computer system until a sum of money is paid) have risen by 195% on small- and medium-sized businesses as of the first quarter of 2019.
The sad truth is that no one really bothers about website security until they face a real threat of malware or ransomware attacks. While individuals have several easy and affordable ways to remain safe on the web, small businesses and even larger companies see that as a cost they don’t want to pay and a complex process they don’t want to learn, so they’re not willing to be proactive.
With this threat looming over every business and service site, it is becoming more critical every day to invest time and money on website security. Because if your website is compromised, your whole business is compromised.
Dive Deeper:
- 9 Effective SEO Techniques to Drive Organic Traffic in 2019
- What Are the Biggest Website Mistakes that Are Lowering My SEO Ranking?
- How Blockchain Can Be Instrumental in Preventing Digital Fraud
- Chapter 1: Blockchain Explained: The Ultimate Peer-to-Peer Network
First Step Towards a Secure Website
The basics of website security begin with SSL/TLS on your existing HTTP.
- SSL stands for Secure Sockets Layer and, in short, it’s the standard technology for keeping an internet connection secure and safeguarding any sensitive data that is being sent between two systems, preventing criminals from reading and modifying any information transferred, including potential personal details.
- TLS stands for Transport Layer Security and is just an updated, more secure version of SSL. We still refer to our security certificates as SSL because it is a more commonly used term, but when you are buying SSL from Symantec you are actually buying the most up-to-date TLS certificates.

What is the difference between HTTP and HTTPS? As per SEOPressor:
- HTTP stands for Hypertext Transfer Protocol. At it’s most basic, it allows for the communication between different systems. It’s most commonly used to transfer data from a web server to a browser in order to allow users to view web pages. It’s the protocol that was used for basically all early websites.
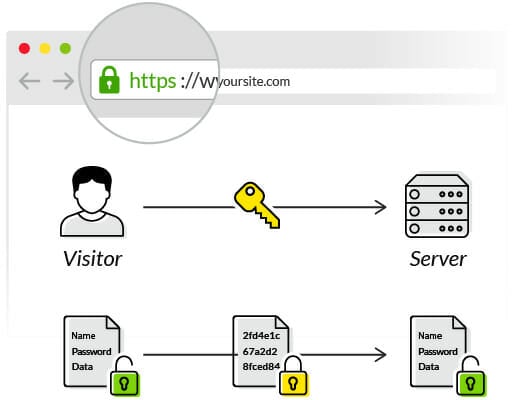
- HTTPS stands for Hypertext Transfer Protocol Secure. The problem with the regular HTTP protocol is that the information that flows from server to browser is not encrypted, which means it can be easily stolen. HTTPS protocols remedy this by using an SSL certificate, which helps create a secure encrypted connection between the server and the browser, thereby protecting potentially sensitive information from being stolen as its transferred between the server and the browser:
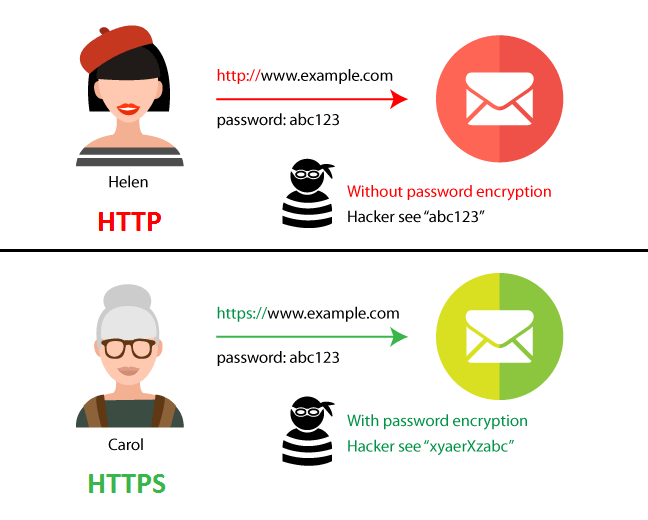
Switching from HTTP to HTTPS is neither complicated nor time-consuming (see “How to Add HTTPS to Your Website” below). With HTTPS, both servers and clients can continue conversing in the same manner, but with complete encryption of their requests and responses (i.e. data):
However, not all is safe and secure with that extra layer of encryption. The SSL certification does not ensure complete security. Even HTTPS sites face their fair share of phishing attacks.
This is the reason that you need to take adequate measures to keep your site safe and not just rely on HTTPS for complete site security.
Dive Deeper:
Is HTTPS a Ranking Signal?
Switching from HTTP to HTTPS is a simple step that can carry your business forward on Google’s SERPs, because Google flags every site as “unsafe” unless it has an HTTPS certification.
At first, HTTPS was a lightweight ranking signal and then over time, Google laid more weight on HTTPS as a ranking signal. As of August 2014, Google announced that HTTPS is a ranking signal:
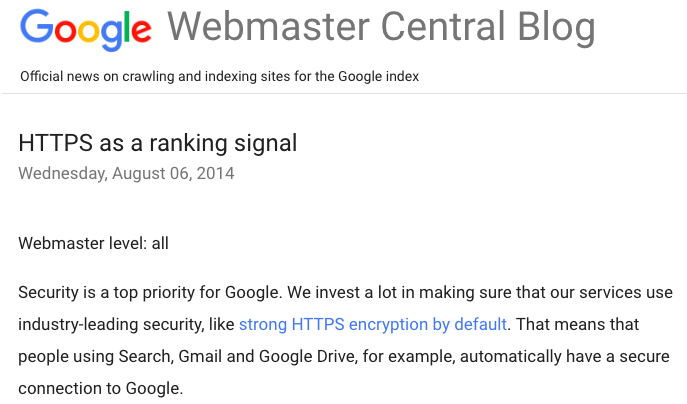
Today, HTTPS is the poster child of trust and security, directly influencing the UX and the SEO of a site. In fact, as of July 2018, all visitors to sites without a TLS certificate receive a “not secure” notification from Google:
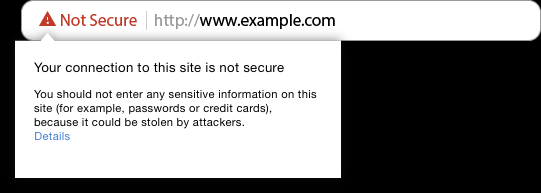
These notifications have resulted in websites without the extra SSL layer seeing reduced traffic and conversion rates. Now it is safe to say that it has become a significant aspect of technical SEO.
Dive Deeper:
- 7 SEO Hacks to Boost Your Ranking in 2019
- 17 Best Free (or Freemium) SEO Tools to Improve Your Ranking
- How (and Why) to Create an Effective Content Structure for Better Ranking
- What Is Enterprise SEO? (Definition, Examples & Tools!)
How to Add HTTPS to Your Website
Here are some easy steps you can follow to switch from HTTP to HTTPS:
Purchase an SSL Certificate
Purchasing an SSL certificate is not that difficult. First, check with your web hosting company. Does your hosting plan includes a certificate? If the pricing and certificate type is in accordance with your requirements, talk to them about adding it to your service.
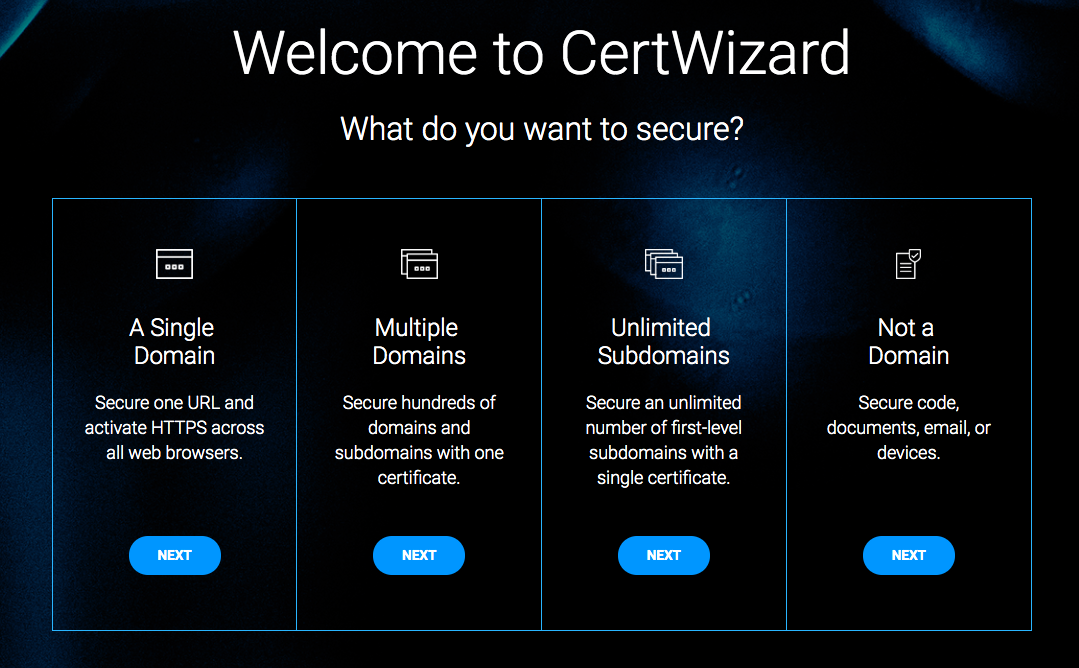
Alternatively, you can look for certificate authorities. Look for preferable pricing and certificate types. Next, purchase and verify your certificate. SSL certificates can be of various types, including DV, OV, EV, Multi-website, and wildcards.
Digicert’s CertWizard can walk you through which type of SSL certificate you need:
Verify and Install the Certificate
Once you have purchased the SSL certificate that meets your requirements, it is time to verify it. The verification can take between a couple of minutes to a few days, depending on your certificate type.
After you receive word from your certification authority, download the files.
The installation process will depend on the source of your certificate. Web hosting services typically take over the installation and streamline the steps for the webmaster.
Here’s how you can install your certificate purchased from outside your web hosting service:
- Log into your web hosting manager account.
- Go to the “Install SSL Certificate” option.
- Enter the SSL certificate, your domain name that needs the SSL and your key (your Certificate Authority should provide you with the key and the SSL certificate).
- Click on “Install”.
Validate the SSL Certificate
The next step is validation, and for that, you need to log out of your web hosting manager and website editor interface. Then, check the address bar – does it show the HTTPS tag? Apart from the HTTPS address, you should be seeing the following:
- A green padlock in the address bar
- Your business name (EV certificates)
- A green address bar (EV certificates)
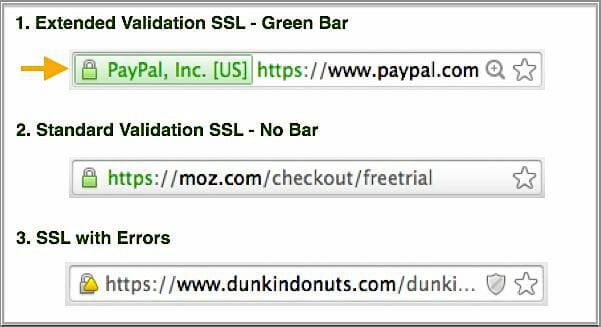
- The onsite security seal of trust or trust badge (depending on certificate type and certification authority):

You should use an SSL checker tool just in case to ensure the status of your website security.
Update Your Website Links
Installing the SSL certificate through the control panel should switch your HTTP site to HTTPS seamlessly. Apart from the main site pages, you need to check other content that has links to your site:
- Social media posts and bios
- Blogs of hosting your site content
- Marketing and sale profiles across the web
- Forum profiles online
- Partner websites that bear a direct link to your site logo
Note: Keep in mind that your old social media, blog posts and embedded links might still direct traffic to the HTTP version of the site, so you need to manually comb through your past off-site posts to fix these old links.
Dive Deeper: How to Fix 15 Common On-Site Technical SEO Issues
Update Your Sitemap
Generating a new XML sitemap is no challenge. You can do so from your Google Analytics account. Check for the default URL of your website in the “Property Settings” under the “Property” option of your Admin account.
Update the http:// to https:// and save the change.
To update the sitemap, visit Webmaster Tools:
- Go to the Search Console
- Click on settings – the gear icon on the top right
- Select “change of address”
Google will take you through the next steps of updating the sitemap, including selecting the new site and confirming 301 redirects. Hit “Submit” once you finish making the changes.
Acquiring and installing an HTTPS certificate is quite straightforward for all website users. The steps we have described above are pertinent to all versions of WordPress and a few other CMS platforms as well.
If you have a reliable web hosting service provider, you should speak to them for quick installation and seamless migration of your site from HTTP to HTTPS by adjusting your hosting plan.
What Lies Beyond HTTPS in the Realm of Cybersecurity?
While HTTPS is essential, it is not all there is to website security. Websites face many different types of cybersecurity threats while running, such as:
1) SQL Injections
An SQL injection is a code injection technique and a nefarious negative SEO technique that a criminal hacker (or your competitor) may deploy to bring down your site. The attacker gains access to the backend of your database by injecting codes into vulnerable or corrupt database content via web page input (such as a user inputting their “username” with an SQL statement). It is still one of the most common threats because it is highly effective.
It can affect any website that uses MySQL, Oracle and SQL servers.
How to Check if Your Website Is under an SQL Injection Attack
To prevent SQL injection attacks, you can run vulnerability scans using trustworthy antivirus software programs. Find out whether the website is experiencing an attack by using a tool such as SQL Injection Test Online.
Follow these rules to prevent SQL injection attacks:
- You should never include the input directly, but sanitize all inputs.
- Only provide the necessary access rights to accounts used for connecting with the database.
- Don’t display SQL statements in error messages; instead, use a generic message.
2) Misconfigurations in Security
Security misconfigurations may include the lack of an SSL certificate, but they typically encompass more factors. They cover almost all types of vulnerabilities that result from the lack of maintenance and update of website applications.
A security misconfiguration can arise from plug-ins that are out-of-date or third-party, unauthorized add-ons to a website. They can provide a window for attackers to exploit sensitive information in a web database. Additionally, database security can be compromised via user privilege abuse, weak authentication or poor data backup practices. Apart from resulting in successful ransomware attacks, this can also result in a complete website shutdown.
How to Reinforce Proper Website Security
Website security begins with HTTPS. However, you need to look deeper into the state of your plug-ins, update your CMS engine, and install security software on your site. Secure configuration needs to be implemented at the application, application server, framework, database server, web server, and platform levels.
These are the most common vulnerabilities that can affect any website today. Updating your site to HTTPS may not be enough to stop these attacks, so you need to think beyond SSL certificates to keep your website database and users safe.
3) CROss-Site Scripting (XSS)
XSS includes the injection of malicious scripts into websites, and is another negative SEO tactic. The attacker leverages a web application to send malicious code to the user in the form of browser script.
The unsuspecting user of the trusted site is likely to click on the code, which gives code access to the user’s cookies, sensitive browser-side information, and session tokens. XSS scripts can also rewrite the content of HTML website pages.
How to Check if Your Website Is under an XSS Attack
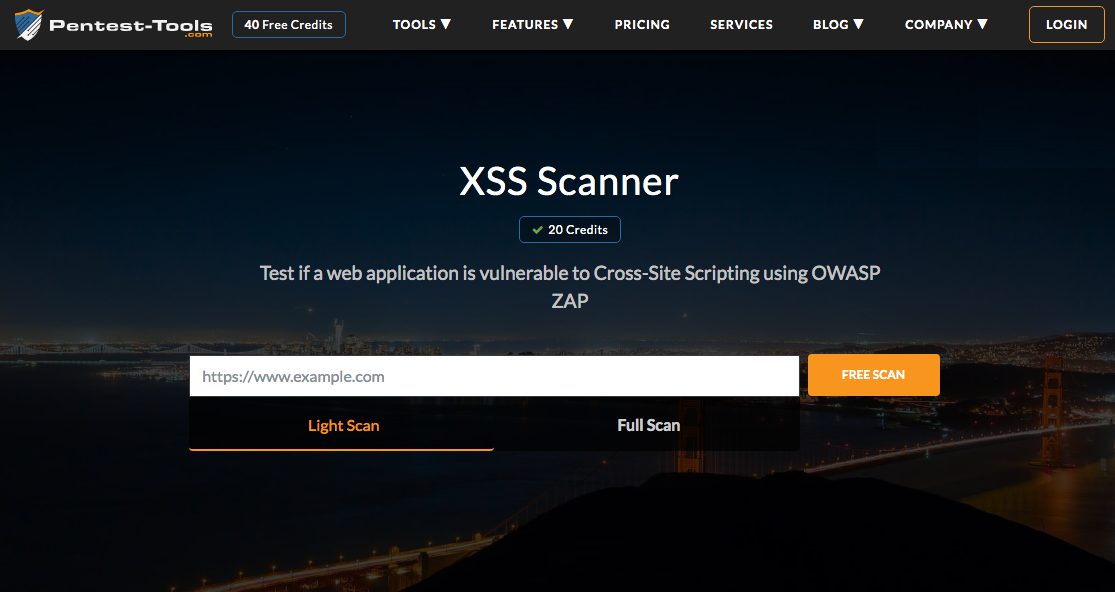
Use a tool such as XSS Scanner:
What to Do to Prevent XSS Attacks
Context-dependent output encoding is necessary to prevent any XSS security. Most modern websites contain an XSS filter. However, they require the correct application of URL encoding.
Webmasters need to allow only links with whitelisted protocols like https:// so no scripts with URL schemes like javascript:// remain barred.
4) CROss-Site Request Forgery
CSRF forces the user to perform actions he or she may not have intended to. It is a malicious attack that targets the state-changing requests on-site.
Leveraging social engineering allows the criminal hacker to trick the end-user into executing actions of the attacker’s bidding. It can include the transfer of funds, providing passwords or changing their email address. If the victim is the admin of a website, a CSRF attack can compromise the website functions of the entire company.
And if you think you’re too smart to get tricked, think again. Check out these common 6 types of social engineering attacks from Norton:
- Baiting
- Phishing/Spear phishing
- Email hacking and contact spamming
- Pretexting
- Quid pro quo
- Vishing
How can you know whether your website is under a cross-site request forgery? Here are OWASP’s guidelines to identify a CSRF.
How to Stop CSRP Attacks
HTTPS is not enough to stop CSRF attacks. The site admin needs to add a hash to the forms, per-request nonce to the forms and URL, and check the referrer header in the HTTP request from the client. Other steps include adding a session identifier to ViewState for.NET scripting.
How Can a Hack Impact a Website’s Organic Traffic and SEO?
Attackers do not discriminate between sites in terms of their size and traffic for attacks. Here’s how it can impact both your traffic and SEO:
Blacklisting
Blacklisting – when your website is removed from the search engines index – is one of the gravest consequences of malware attacks. Since most websites do not receive any notification, they can be repeatedly targeted for ransomware and malware attacks. Several websites have persistent vulnerabilities that make them prone to SQL injections, XSS, CSRF and phishing attacks.
Not receiving any notification can mean a continual loss of money, reputation and visitors when Google spots the anomalous behavior and blacklists the site. Finding yourself on the blacklist is the end of all traffic and SEO for any website. However, it is one way to begin from square one with a clean site.
Errors in Crawling
Scraper bots crawl sites to scrape content, block search engine bots, and engage in data theft. Your SERP rankings can also take a hit when scraper bots create duplicate content on another location. They can create 404 and 503 errors in your Google Search Console. They are responsible for creating resource intensive infinite loops.
Upon finding duplicate content, file a DMCA complaint with Google. Routine analysis of log files with premium tools can produce an exhaustive list of bots crawling your site. Identify their source to segregate the good bots from the bad ones.
Dive Deeper: Google to Stop Supporting Robots.txt Noindex: What That Means for You
SEO Spam
Criminal hackers can achieve SEO spam through SQL injections, which can result in the blacklisting of your website or complete alteration of how your site appears in the Google SERPs. They can also reduce your website speed, which is one of the top ranking signals.
You need security plug-ins and SEO tools that can spot malicious activity in real-time on your site. Patching the vulnerabilities is absolutely essential. Check out paid platforms that offer wholesome monitoring of websites, such as Sucuri, an industry leader in WordPress security (it’s a paid service, but they offer limited WordPress scanning for free).
Final Thoughts
At the end of the day, you mustn’t make Google your antivirus. Google flags unreliable sites and blacklists the ones that pose a threat to users, but relying on Google’s updates is not a proactive way to care for your site’s security and SEO.
If you want to enhance your SEO and improve your website traffic, always begin with HTTPS. Then, think about investing in a website surveillance system that monitors beyond the SSL certification of your site.